ARP Poisoning, MAC Spoofing & MITM Attacks Explained
Three attacks. One goal. Every one of them designed to put an attacker silently between you and the network you trust. ARP poisoning, MAC spoofing, and IRDP manipulation are among the most powerful interception techniques in a hacker’s toolkit and understanding how they work is the first step toward stopping them.
ARP Poisoning: Lying to the Network
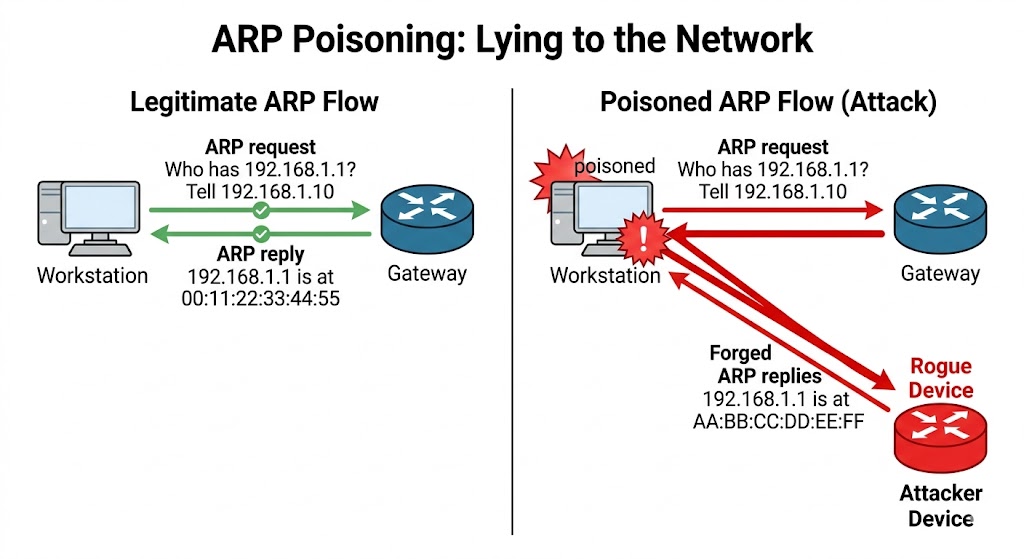
Every device on a network needs to know the MAC address of the device it wants to talk to. That is what ARP Address Resolution Protocol is for. It is a simple, stateless protocol that maps IP addresses to MAC addresses. When your laptop wants to send data to another device, it checks its ARP cache. If the MAC address is not there, it broadcasts an ARP request asking “who has this IP?” The device with that IP replies with its MAC address, and communication begins.
Here is the critical flaw: ARP has no authentication. Any device can send an ARP reply at any time, even without being asked. And every device that receives that reply will update its ARP cache without questioning whether the reply is genuine.
Attackers exploit this by flooding the network with fake ARP replies that associate their own MAC address with a legitimate IP typically the gateway. Every device that receives the spoofed reply updates its ARP cache with the wrong mapping. All traffic intended for the gateway now flows to the attacker’s machine instead. The attacker reads it, forwards it on, and the victim never notices. This is a classic Man-in-the-Middle attack executed entirely through ARP.
The threats that ARP poisoning enables include:
• Packet Sniffing — sniffs traffic over the network or a part of the network
• Session Hijacking — steals valid session information to gain unauthorized access to an application
• VoIP Call Tapping — monitors all VoIP network traffic and picks only the VoIP traffic by MAC address
• Data Manipulation — captures and modifies data or stops the flow of traffic entirely
• Stealing Passwords — tricks target hosts into sending usernames and passwords through forged ARP replies
• DoS Attack — links multiple IP addresses to a single MAC address, overloading the target with traffic
Tools used for ARP poisoning include: arpspoof, Habu, bettercap, Ettercap, RITM, ARP Spoofer, and larp.
How to Defend Against ARP Poisoning
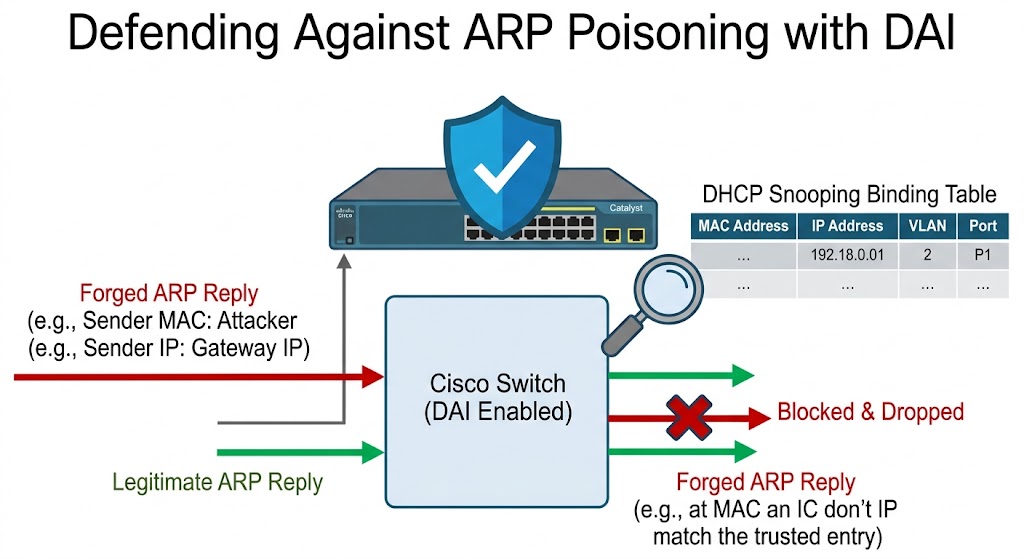
The primary defense is Dynamic ARP Inspection (DAI). It works hand in hand with DHCP snooping.
When DAI is enabled on a VLAN, every ARP packet passing through an untrusted port is checked against the DHCP snooping binding table a database of known MAC address, IP address, and VLAN interface mappings. If an ARP reply claims that a certain IP belongs to a certain MAC but that combination does not exist in the binding table, the packet is discarded immediately. The MITM attack is stopped before the ARP cache is ever poisoned.
For networks with static IP addresses where DHCP snooping is not possible, static ARP entries can be configured manually to prevent the cache from being overwritten by forged replies.
Configuring DAI on a Cisco switch — DHCP snooping must be enabled first:
Switch(config)# ip dhcp snoopingSwitch(config)# ip dhcp snooping vlan 10Switch(config)# ^ZSwitch(config)# ip arp inspection vlan 10Switch(config)# show ip arp inspectionARP spoofing detection tools include: Wireshark, Capsa Portable Network Analyzer, OpUtils, netspionage, NetProbe, and ARP-GUARD.
MAC Spoofing: Stealing an Identity
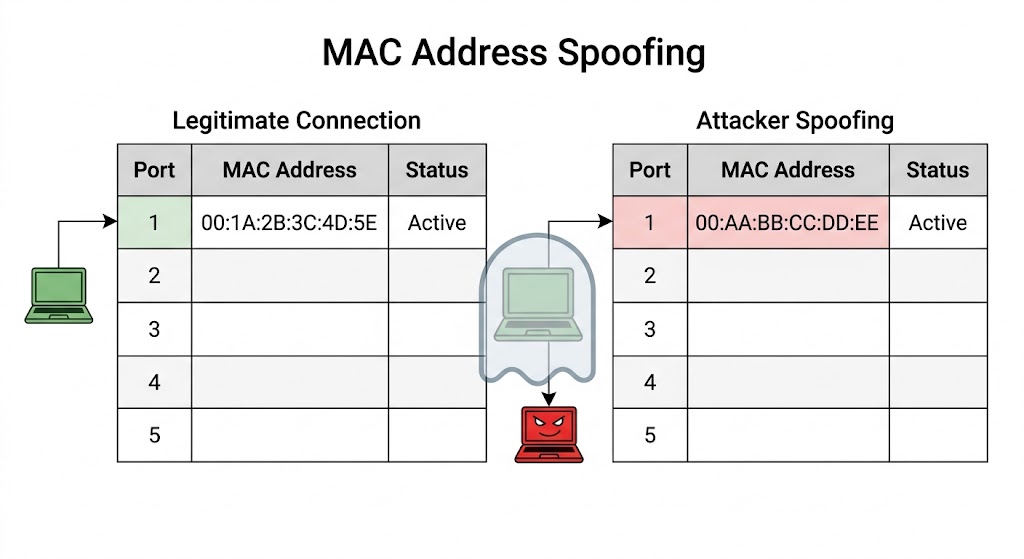
MAC spoofing also called MAC duplicating takes a different approach. Instead of poisoning the ARP cache, the attacker sniffs the network to find the MAC address of a legitimate device currently connected to a switch port. They then configure their own NIC to use that exact MAC address.
The switch sees two devices claiming the same MAC address. Depending on timing and traffic, the switch may start routing the legitimate device’s traffic to the attacker’s port instead. The attacker receives everything intended for the real user login sessions, file transfers, emails without manipulating a single ARP table.
This technique can also bypass wireless access points that filter connections by MAC address. The attacker simply copies a whitelisted MAC and connects freely making MAC address whitelisting alone an unreliable security control.
On Windows, MAC spoofing can be done through:
• Network Settings → Ethernet Properties → Configure → Advanced → Network Address — type in the new MAC directly
• Registry Editor at HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Class by adding a NetworkAddress value to the relevant adapter subkey
Tools like MAC Address Changer make this even simpler a single click generates a random MAC or allows manual entry of any target address.
IRDP Spoofing: Redirecting the Gateway
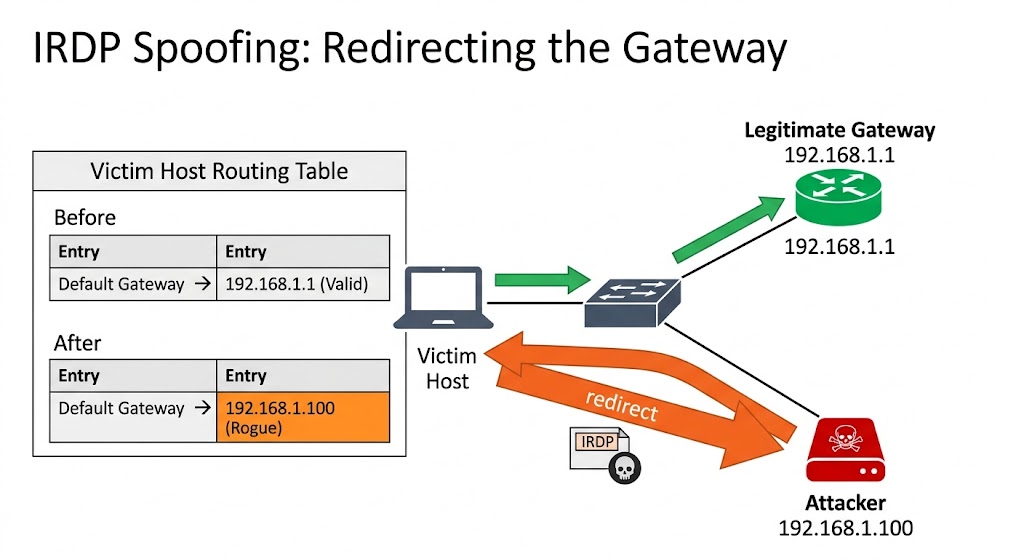
IRDP Internet Control Message Protocol Router Discovery Protocol allows hosts to discover routers on their network automatically. When a host receives an IRDP router advertisement, it updates its routing table to use that router as the default gateway.
An IRDP spoofing attack works by sending forged IRDP router advertisement messages claiming that the attacker’s machine is the default gateway. Victims update their routing tables without question. All outbound traffic now flows through the attacker first. The attacker captures everything, forwards it to the real gateway, and the victim’s internet connection appears completely normal.
What makes IRDP spoofing particularly dangerous is that it operates at the routing layer it does not touch the ARP cache at all. Defending against it requires:
• Disabling IRDP on hosts that do not need it
• Using static default gateway configuration where possible
• Monitoring the network for unexpected IRDP router advertisements
The Common Thread
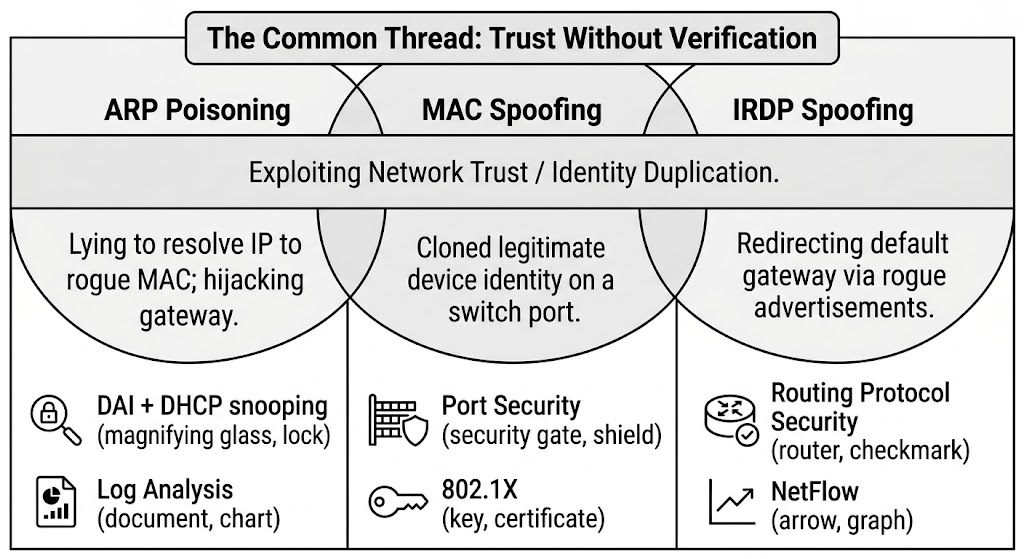
ARP poisoning, MAC spoofing, and IRDP spoofing all exploit the same fundamental weakness: trust without verification. ARP trusts any reply. Switches trust any MAC. Routing tables trust any router advertisement. These protocols were designed in an era when the assumption was that everyone on the network was legitimate.
That assumption no longer holds. Every one of these attacks is an active sniffing technique which means they can be detected with the right monitoring tools. DAI, DHCP snooping, static ARP entries, and careful network monitoring are your defenses. None of them are complex to configure. All of them are worth the effort.
Things to Keep in Mind
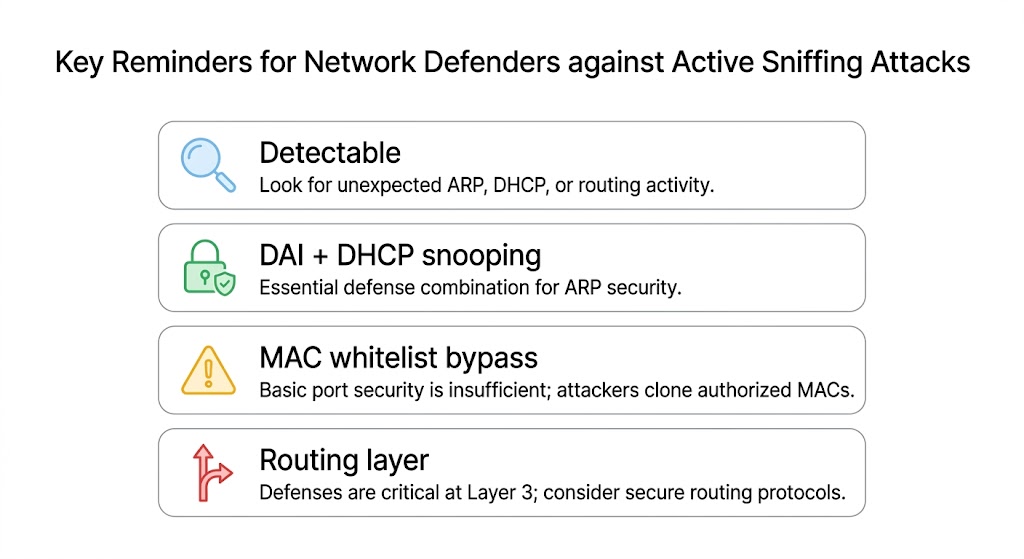
• ARP poisoning, MAC spoofing, and IRDP attacks are active techniques and leave traces unlike passive sniffing which is nearly impossible to detect
• Dynamic ARP Inspection must be paired with DHCP snooping to work enable DHCP snooping first
• MAC spoofing can bypass wireless MAC filtering entirely MAC address whitelisting alone is not a reliable security control
• IRDP spoofing is particularly stealthy because it redirects traffic at the routing layer without touching the ARP cache
Want to dive deeper?
Explore our certified internship and certification programs related to this topic.

Edwin Saji
Intern at Edwhere