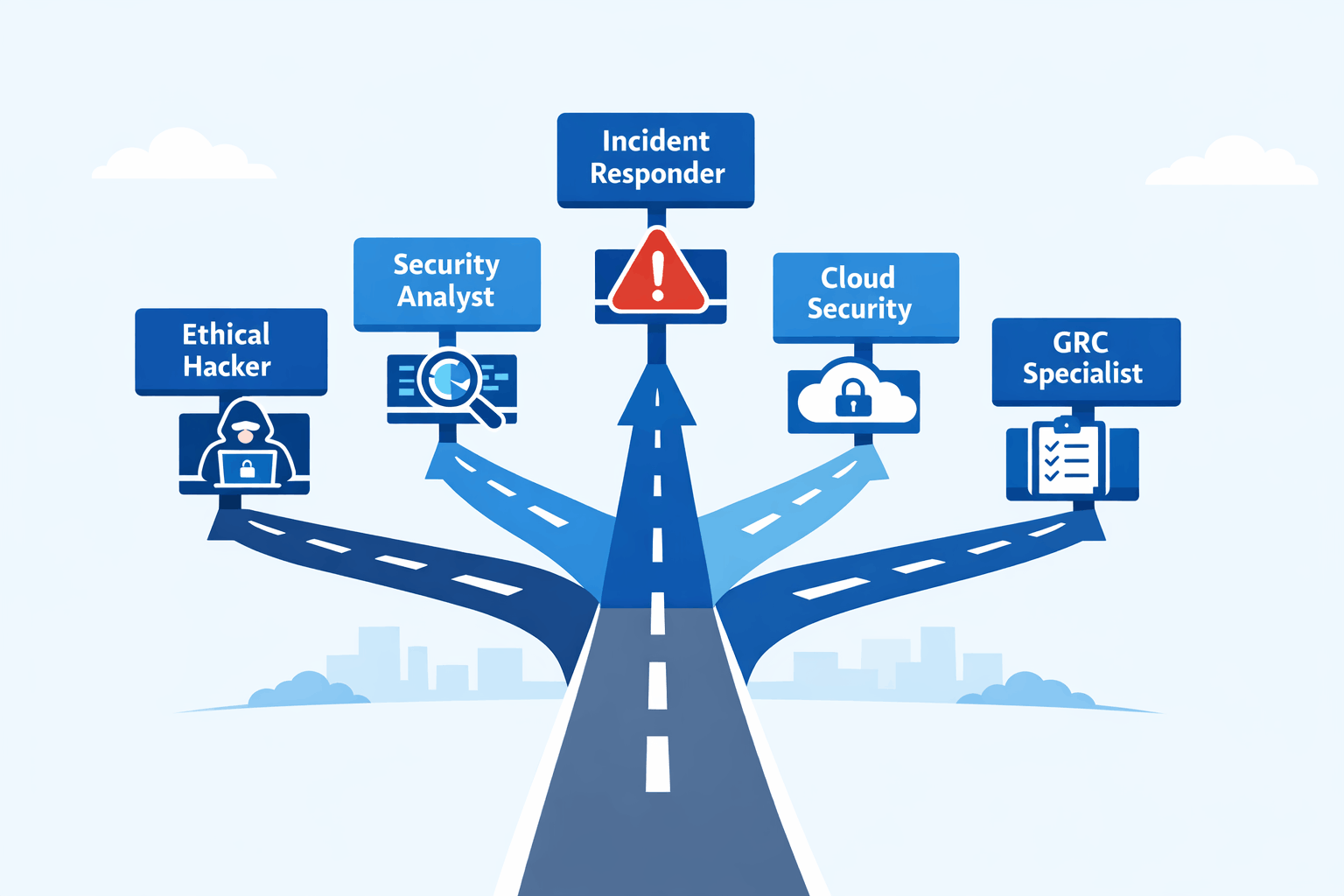
Cybersecurity Job Roles: What You Can Become (2026)

Cybersecurity is one of the fastest-growing fields in tech — but most people only know about ethical hacking. The reality is much broader. Here is a clear breakdown of the most in-demand roles in 2026 and how to work toward them.
Ethical Hacker / Penetration Tester
Hired by companies to attack their own systems legally and report what they find. The goal is to find weaknesses before real attackers do.
Skills: Networking, Linux, Burp Suite, Nmap, Metasploit.
How to start: Practice on HackTheBox or TryHackMe. Work toward CEH or OSCP.
Security Analyst
Monitors systems and networks for threats in real time. Reviews alerts, investigates incidents, and responds to attacks. One of the most common entry-level roles in the field.
Skills: Log analysis, network monitoring, SIEM tools like Splunk.
How to start: Learn networking basics and get familiar with SIEM platforms. CompTIA Security+ is a good starting certification.
Incident Responder
Called in when something goes wrong — a breach, ransomware attack, or unauthorized access. Their job is to contain the damage, investigate what happened, and restore operations.
Skills: Digital forensics, malware analysis, log investigation.
How to start: Study how attacks unfold and practice on BlueTeamLabs Online.
Cloud Security Engineer
Secures cloud infrastructure on platforms like AWS, Azure, and Google Cloud. Manages configurations, access controls, and data security in cloud environments.
Skills: Cloud platforms, identity and access management, network security.
How to start: Get familiar with one cloud platform and work toward AWS Security Specialty or Microsoft AZ-500.
GRC Analyst
Not every cybersecurity role is technical. A GRC analyst ensures the organization follows the right security policies, manages risk, and meets compliance requirements like ISO 27001 and GDPR.
Skills: Risk assessment, compliance frameworks, documentation, communication.
How to start: Study compliance frameworks and consider certifications like CISA or CRISC.
How to Build Experience Without a Job
This is the most common stumbling block for beginners: you need experience to get hired, but you need a job to get experience. The good news is that cybersecurity has one of the most active self-learning ecosystems of any tech field.
Here is a practical progression path:
Start with the fundamentals. Before touching tools like Metasploit or Splunk, invest time in understanding how networks actually work the TCP/IP model, DNS, HTTP, firewalls, and routing. Professor Messer's free CompTIA resources and the free tier on TryHackMe are excellent starting points that require no prior experience.
Build a home lab. A basic lab setup using free tools like VirtualBox or VMware lets you run virtual machines to practice attacks and defenses in an isolated environment. Set up a vulnerable machine like Metasploitable2 and practice exploiting it legally. This hands-on time is far more valuable to employers than theoretical knowledge alone.
Document everything publicly. Create a blog or GitHub repository where you write up challenges you have solved, labs you have completed, and concepts you have learned. Employers and recruiters actively search these a well-maintained write-up portfolio has helped many candidates break into their first role without formal experience.
Participate in CTFs. Capture the Flag competitions are timed events where participants solve security puzzles across categories like web exploitation, reverse engineering, and cryptography. Platforms like CTFTime list competitions year-round, and many are beginner-friendly. Competing in a few CTFs and noting them on your resume signals practical ability immediately.
Soft Skills That Are Often Overlooked
Technical ability gets you into the interview. Communication gets you the job and advances your career. Cybersecurity professionals regularly brief non-technical executives, write incident reports, and explain vulnerabilities to development teams who may not share their background.
Invest time in learning how to write clearly and speak with confidence about technical topics to a non-technical audience. Practice translating jargon into plain language. Many engineers underestimate this, but the professionals who move into senior and leadership roles quickly are almost always the ones who can bridge the gap between technical and business thinking.
Which Role Is Right for You?
• You enjoy breaking things and finding flaws — Penetration Tester or Bug Bounty Hunter
• You prefer monitoring and responding to threats — Security Analyst or Incident Responder
• You want to work across cloud infrastructure — Cloud Security Engineer
• You prefer policy and compliance work — GRC Analyst
Things to Keep in Mind
• You don’t need to choose a specialization immediately. Start broad and specialize as you gain experience.
• Practical skills matter more than certifications. Employers in 2026 want hands-on experience.
• Kerala’s tech sector — Technopark and Infopark — has real demand for security analysts, penetration testers, and cloud security professionals.
Want to dive deeper?
Explore our certified internship and certification programs related to this topic.

Edwin Saji
Intern at Edwhere