Inside an IoT Attack: How Smart Devices Get Hacked

Your smart speaker is listening. Your security camera is watching. Your thermostat knows when you are home and when you are not. These devices were sold with the promise of making life easier and they do. But they were rarely sold with the promise of being secure. And most of them are not.
In 2026, there are over 21 billion IoT devices connected to the internet globally. Routers, cameras, baby monitors, industrial sensors, hospital equipment, smart TVs. Every single one of them is a potential entry point. Attackers do not break down the front door. They walk through the back door that the manufacturer left unlocked.
Why IoT Devices Are So Easy to Attack
A laptop can run antivirus software, receive security patches, and enforce complex authentication policies. An IoT device usually cannot. The CPU is too slow. The memory is too small. The storage is too limited. There is no room for a full security stack on a device that costs fifteen dollars and runs on a coin battery.
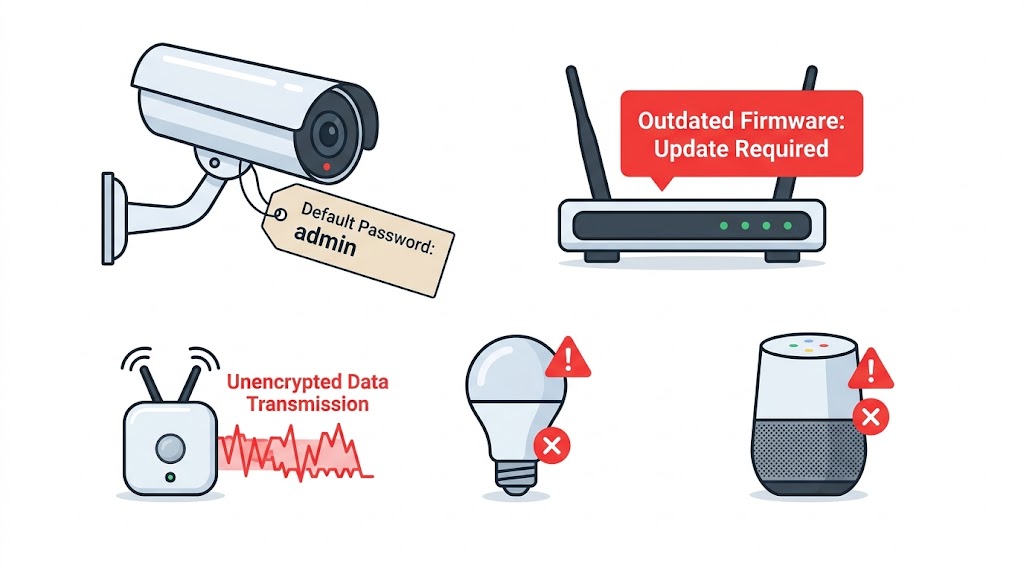
This creates a security gap that attackers have learned to exploit consistently. The five weaknesses that make IoT devices such attractive targets are:
• Default credentials — most IoT devices ship with a username and password like admin/admin or root/password. Millions of users never change them. Attackers know every default credential for every popular device and scan for them automatically.
• Outdated firmware — unlike phones and computers, IoT devices often never receive security updates. A vulnerability discovered in 2019 may still be unpatched on a camera running in a hospital today.
• No encryption — many IoT devices transmit data in plain text. Commands sent to a smart lock or a sensor can be intercepted and read, or worse, replayed and manipulated.
• Always on, always connected — these devices run continuously and are directly reachable from the internet, making them perpetually exposed. Research shows most internet-connected devices are probed by attackers within minutes of going online.
• No security monitoring — nobody is watching what a smart fridge is doing on the network at 3am. IoT devices operate in blind spots that traditional security tools were never designed to cover.
How the Attack Actually Happens

It starts with a scan. Attackers run automated tools or use services like Shodan, which indexes internet-connected devices to find IoT devices with open ports. A camera on port 23 (Telnet) with default credentials is not a target. It is a guaranteed entry.
The attacker connects. They try the default username and password for that device’s manufacturer. If it works and it does far more often than it should they now have root access to a device sitting inside someone’s home or office network. From there, the attack can go in several directions.
From One Device to the Entire Network
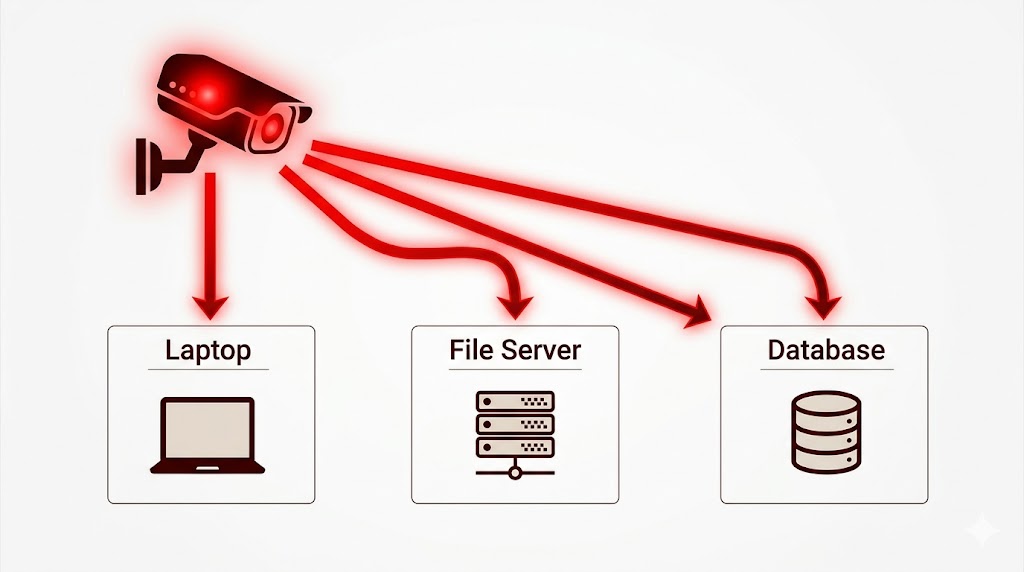
The IoT device itself may not contain anything valuable. But it sits on the same network as the laptop, the file server, the corporate database, or the hospital’s patient records system. Once an attacker is inside the device, they use it as a launchpad.
This is called lateral movement. The attacker scans the internal network from inside the compromised device invisible to external firewalls because the traffic looks like it is coming from a trusted internal device. They find other systems, exploit vulnerabilities, escalate privileges, and move deeper.
In 2024, the Akira ransomware group was documented using compromised IoT cameras to bypass endpoint detection and response tools on corporate networks. The cameras could not run EDR agents. They were blind spots. The attackers used them to move laterally and deploy ransomware before anyone noticed.
The Botnet Problem: Your Device Working for Someone Else
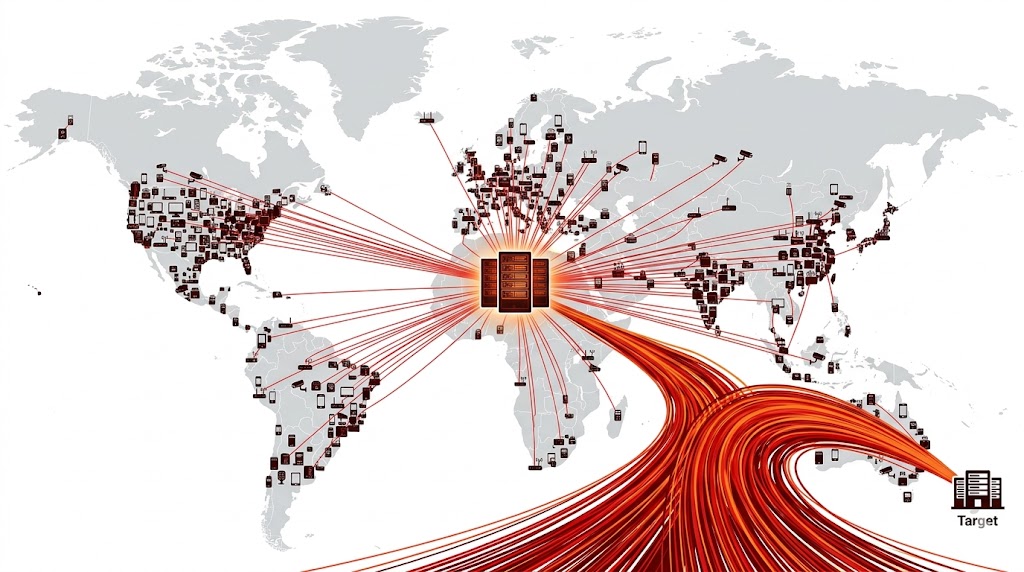
Not every attacker wants to steal data from the network. Sometimes the device itself is the prize not for what it contains, but for what it can do when combined with millions of others.
In 2016, the Mirai botnet infected hundreds of thousands of IoT cameras and DVRs using default credentials and used them to launch one of the largest DDoS attacks ever recorded, taking down Twitter, Netflix, Reddit, and CNN. The devices’ owners had no idea. Their cameras were still working. The footage was still recording. But in the background, their devices were firing massive volumes of junk traffic at targets around the world.
In March 2026, the US Department of Justice disrupted four IoT botnets AISURU, Kimwolf, JackSkid, and Mossad that together comprised over 3 million infected devices and had launched DDoS attacks peaking at 31.4 Tbps. These were not exotic malware campaigns. They were built almost entirely from devices with default or weak credentials and unpatched firmware.
When IoT Attacks Cross into the Physical World

Most cyberattacks stay digital. IoT attacks do not always have that luxury.
In March 2026, Iranian-linked threat actors were documented hijacking Hikvision and Dahua security cameras across multiple countries in the Middle East, timed to coincide with missile strikes. The cameras were being used for real-time battlefield reconnaissance watching where missiles landed, assessing damage, guiding follow-on strikes. The same devices sold to businesses and homes for protection were being turned into tools of war.
In the healthcare sector, breaches involving connected medical devices now average over $10 million in damage per incident the highest cost of any sector. One in five medical devices runs an unsupported operating system. Seventy-seven percent of hospital systems contain known exploited vulnerabilities. These are not edge cases. They are the norm.
How to Defend Your Devices
The good news is that the most effective defenses are not complicated. The majority of successful IoT attacks exploit the same handful of weaknesses, and closing them closes most of the attack surface.
• Change default credentials immediately — every device, every time. Use a strong, unique password for each one. This single step would have prevented the majority of IoT attacks on record.
• Update firmware regularly — check for firmware updates and apply them. If a device no longer receives updates from the manufacturer, treat it as compromised and replace it.
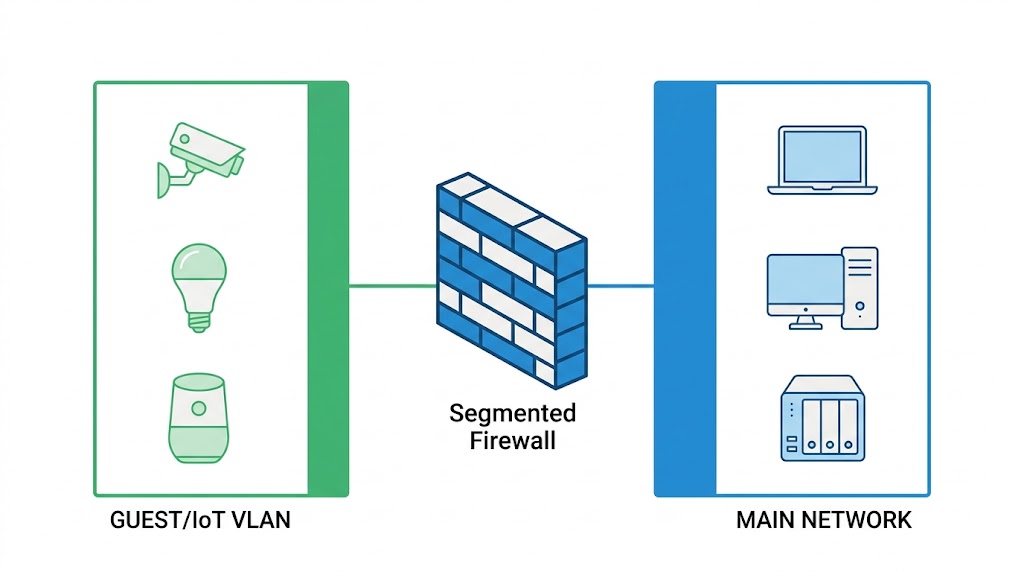
• Segment your network — put IoT devices on a separate VLAN or guest network. If one gets compromised, it cannot reach your main devices, files, or servers.
• Disable unused ports and services — Telnet, FTP, and other unencrypted services should be disabled unless specifically needed. Every open port is a potential entry point.
• Monitor device traffic — a camera that suddenly starts scanning internal IP addresses or communicating with an unfamiliar server is a device that has been compromised. Network monitoring catches this. Ignoring IoT traffic does not.
Things to Keep in Mind
• IoT devices cannot run traditional security software network-level controls are the only reliable defense
• By late 2025, IoT malware incidents were up 124% compared to the year before the threat is accelerating, not slowing
• The EU Cyber Resilience Act begins enforcement in September 2026, requiring manufacturers to report actively exploited vulnerabilities within 24 hours regulatory pressure is finally arriving
• Default credentials and unpatched firmware account for the vast majority of successful IoT attacks fixing these two things closes most of the risk
• IoT security is not just a home user problem hospitals, factories, governments, and power grids are all running vulnerable connected devices at scale
Want to dive deeper?
Explore our certified internship and certification programs related to this topic.

Edwin Saji
Intern at Edwhere