Why Every BCA Student Should Do a Cybersecurity Internship Before Graduation

You are in the middle of your BCA program. You have studied networking, programming, and maybe even dipped into ethical hacking. But here is the honest truth — reading about cybersecurity and actually doing cybersecurity are two completely different things.
The gap between classroom knowledge and industry readiness is real. And the one thing that closes it faster than anything else is a proper, hands-on internship in a field that actually matches where the jobs are.
Cybersecurity is one of the fastest-growing fields in the world right now. The demand for skilled professionals far outpaces the supply. Companies are not waiting for perfectly polished candidates. They are looking for people who have actually used the tools, worked on real problems, and know how a professional environment operates.
That is exactly what the right internship gives you.
Who Is Edwhere?

Edwhere is a Kerala-based cybersecurity and technology education company founded in 2019 with one clear purpose: to make practical, industry-ready knowledge accessible to students in a form that is understandable and directly applicable.
In seven years, Edwhere has grown from a small team into an organization that has trained over 40,000 students across more than 10 specialized courses. It is EC-Council accredited, ISO9001 certified, and operates according to NIST standards the same frameworks used by cybersecurity professionals globally.
Edwhere has worked with organisations that most cybersecurity students only read about:
• Kerala Police Cyberdome — the state’s premier cyber intelligence and investigation hub
• Engineering colleges and universities across Kerala for faculty development and student training programs
• National and international technology clients including Labour India Magazine and various tech organisations
Edwhere’s training covers cybersecurity and ethical hacking, IoT security, IT and networking, data analytics, and electronics. The approach across all programs is the same: theory is kept minimal, and hands-on lab time is maximised.
With 33,000+ subscribers on YouTube (Safeonnet) and a dedicated learning app on the Play Store, Edwhere has built one of the most active cybersecurity learning communities in Kerala a community that includes jobs, internships, research, entrepreneurship, and mentorship channels for students at every level.
What Makes Edwhere Different from a Regular Training Center
Most training centers teach you concepts. Edwhere teaches you how to work. That distinction matters enormously when you step into a job interview or an actual security role.
The programs at Edwhere are built around three principles:
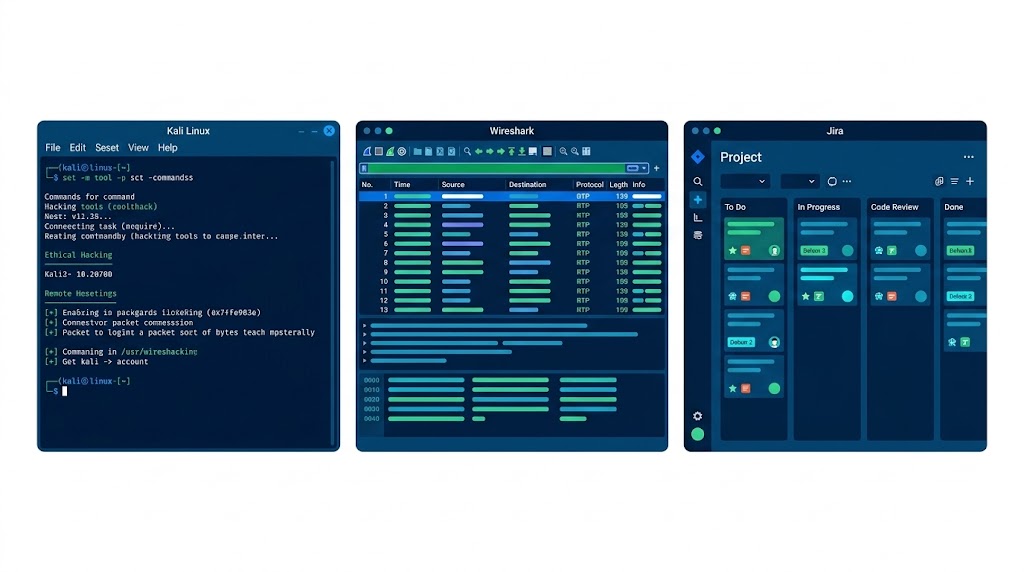
• Real tools — students work with the same tools used by professional penetration testers and security analysts: Kali Linux, Nmap, Wireshark, Burp Suite, Binwalk, and more
• Real environments — lab setups simulate actual corporate and IoT environments, not simplified textbook scenarios
• Real documentation — students write reports, submit findings, and communicate through professional tools like Jira and Slack, exactly as they would in an industry role
Edwhere runs workshops, hands-on STTP (Short-Term Training Programs), faculty development programs, and beginner-to-advanced cybersecurity courses. Whether you are just starting out or preparing for a certification like CEH, there is a structured path for you.
The Internship: What You Actually Do
Edwhere offers an 8-week, 240-hour Industry-Immersive Cybersecurity Internship focused on IoT security one of the most in-demand specializations in the field right now.
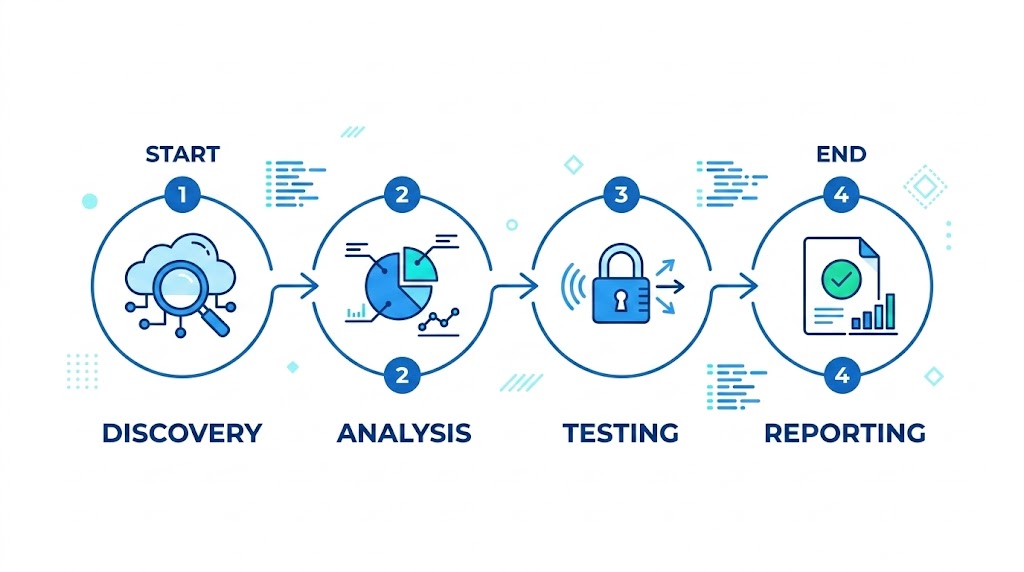
The program is built to convert beginners into Junior Security Analysts. It does not assume you already know everything. It builds you up systematically across four phases:
Phase 1 — Discovery
You start by understanding how IoT devices and cloud systems communicate the architecture, the protocols, the data flows. This is the foundation everything else builds on.
Phase 2 — Analysis
You move into firmware analysis pulling apart the software that runs inside IoT devices to find vulnerabilities. This is real security research, not a simulation.
Phase 3 — Testing
You analyse network traffic and protocols using professional tools. You run actual scans, intercept communications, and identify weaknesses in a controlled lab environment.
Phase 4 — Reporting
You document everything. You write structured findings, suggest remediation steps, and present your work exactly as a security analyst would deliver a report to a client or employer.
Every day follows a structured professional model: a morning stand-up meeting and theory session, followed by an afternoon of hands-on lab work and project execution, ending with end-of-day reporting. This is not a passive learning experience. You are expected to show up, contribute, and deliver.
Tools You Will Work With
By the end of the internship, you will have hands-on experience with tools that appear in every cybersecurity job description:
• Kali Linux — the industry-standard penetration testing operating system
• Nmap — network mapping and port scanning
• Binwalk — firmware extraction and analysis for IoT devices
• Wireshark — network traffic analysis and packet capture
• Jira — professional project tracking and task management
• Slack — team communication in a professional workflow
How This Fits Your BCA Program
If you are a BCA (Honours) student under an FYUGP-aligned program, an internship is not optional it is a mandatory credit requirement.
The university requires students to complete an industry internship after the 4th semester. The 240-hour Edwhere program fulfills the 4-credit internship requirement exactly. You work with an industry mentor who guides your progress and evaluates your performance, while your college supervisor tracks your participation.
Your final output an internship report and presentation is evaluated on work quality, documentation, attendance, and the depth of your technical findings. The structure of the Edwhere program is built precisely to help you produce that output well.
Why IoT Security Specifically?

IoT security is not a niche anymore. With over 21 billion connected devices in the world and attack incidents against smart devices growing by over 124% year on year, every organisation that runs connected infrastructure needs people who understand how these devices are compromised and how to defend them.
The skills you build in an IoT security internship directly translate to careers in penetration testing, bug bounty hunting, security analysis, and incident response. These are not entry-level roles that disappear in a few years. They are the foundation of the cybersecurity industry.
How You Are Evaluated
The internship evaluation covers five areas that reflect exactly what employers look for:
• Professionalism — attendance, discipline, and meeting daily commitments
• Learning — understanding of concepts covered each week
• Technical Skills — practical ability with tools like Nmap and Binwalk
• Discovery Skills — ability to map attack surfaces and identify vulnerabilities
• Documentation — quality and clarity of written reports and findings
This is not a checkbox exercise. Every criterion is something a hiring manager would care about on day one of a real job.
Is This the Right Next Step for You?
If you are a BCA student who wants to go beyond theory, build a portfolio of real security work, satisfy your university internship requirement, and step into the cybersecurity job market with actual experience this is exactly what an Edwhere internship is designed for.
The cybersecurity field does not wait. The students who start building real experience now are the ones who will have options when they graduate.
Learn more about Edwhere’s programs and the internship at learn.edwhere.com or call +91 81380 41614.
Things to Keep in Mind
• The internship cannot be done at your own college — it must be an external industry placement
• 240 hours fulfills the 4-credit university requirement for BCA Honours students
• You get both a college supervisor and an industry mentor — guidance from both sides throughout the program
• The final output is an internship report and viva presentation — the structured daily reporting at Edwhere prepares you for this directly
• IoT security knowledge applies directly to bug bounty, penetration testing, and security analyst roles
Want to dive deeper?
Explore our certified internship and certification programs related to this topic.

Edwin Saji
Intern at Edwhere