Network Sniffing : Hubs, Switches & How Attackers Intercept Your Data

Every time you send data online, it travels as small packets. Most people assume only the intended recipient sees them. But in the right conditions, someone on the same network can silently intercept every one of them. That is called network sniffing.
What is packet sniffing?
A packet sniffer captures and reads all data packets on a network by switching the network card into promiscuous mode meaning it accepts all traffic, not just traffic addressed to it. Attackers can steal passwords, emails, FTP credentials, DNS queries, chat sessions, and account information from a single point.
Think of it like this. In a normal conversation at a coffee shop, you whisper to the person next to you and nobody else hears. Packet sniffing is the digital equivalent of someone at a nearby table recording everything you say, without you ever knowing they are there.
How does a sniffer work?
Every device has a MAC address and an IP address. Traffic is routed using MAC addresses. If a device doesn't know the destination's MAC, it sends an ARP broadcast to the whole network. Sniffers exploit this depending on whether the network uses a hub or a switch.
When a sniffer is active, it sits quietly in the background. It does not send traffic. It does not knock on doors. It simply listens and reads everything that flows past it. The NIC accepts frames it would normally discard, hands them to the software, and the attacker gets a live view of every conversation on the network.
Hub-based networks — passive sniffing

In a hub-based network, every packet is broadcast to all devices. A sniffer in promiscuous mode simply reads everything without checking the destination. This is passive sniffing the attacker sends no traffic, just listens. It leaves no trace and is nearly impossible to detect.
Hubs are largely obsolete in modern networks, but they still exist in older office environments and industrial systems. Whenever a hub is present, passive sniffing is trivially easy. The attacker simply connects, enables promiscuous mode, and watches. No manipulation required.
Switch-based networks — active sniffing
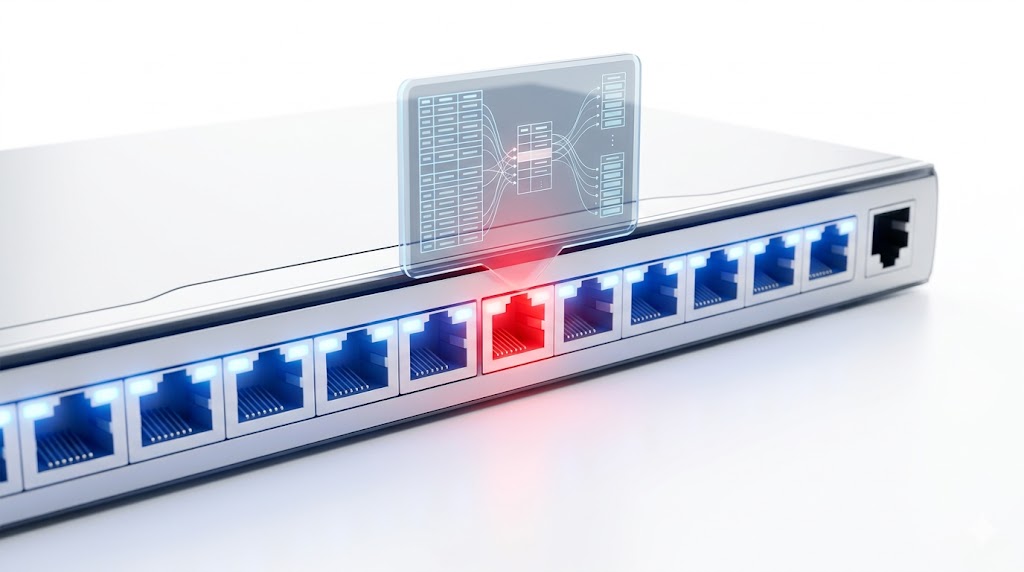
A switch uses a CAM table to send traffic only to the correct port so passive sniffing doesn't work. Attackers instead use active sniffing to manipulate the network:
• MAC flooding — overflows the CAM table so the switch broadcasts to all ports like a hub
• ARP spoofing — sends fake ARP replies to redirect traffic through the attacker's machine
• DNS poisoning — corrupts DNS so domain names point to the attacker's IP
• Rogue DHCP server — hands out false network settings to clients
• Switch port stealing — floods the switch with the victim's MAC to hijack their traffic
Active sniffing can be detected with proper monitoring. Unlike passive sniffing, these techniques inject traffic and leave traces in network logs. This is why active sniffing is harder to execute cleanly but also why it is the technique most commonly used against modern switched networks.
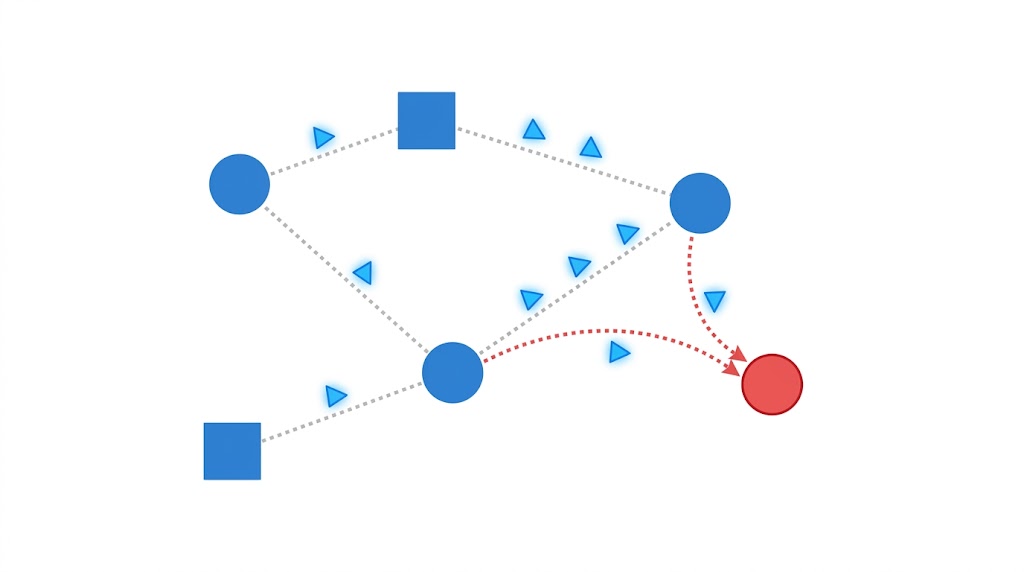
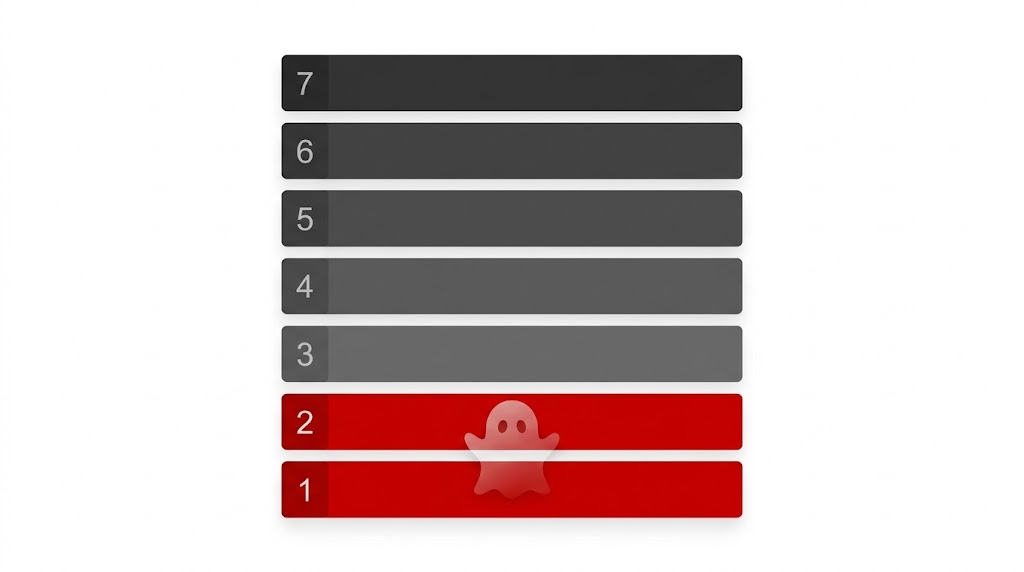
How an attacker intercepts your traffic

1. Attacker connects to an available port on the target network
2. Scans the network to find the target machine
3. Uses ARP spoofing to redirect the victim's traffic through their machine
4. All packets now flow through the attacker a classic Man-in-the-Middle (MITM) attack
5. Attacker captures passwords, usernames, credit cards, and session cookies
The victim’s screen looks completely normal the entire time. Pages load. Emails send. Nothing appears wrong. The attacker is simply sitting in the middle of every conversation, reading it all.
Protocols vulnerable to sniffing
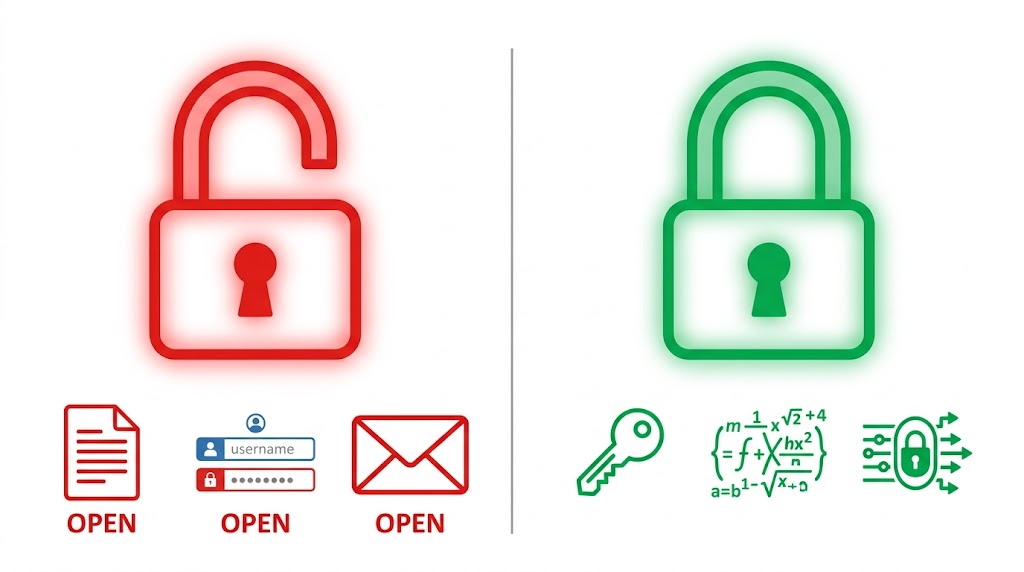
These transmit data in cleartext with no encryption:
• Telnet and Rlogin — usernames, passwords, and keystrokes fully exposed
• HTTP — all user data sent in plaintext
• FTP — credentials and file transfers completely unprotected
• SMTP, POP, IMAP — email sent in cleartext
• SNMP v1/v2 — network management with no encryption
• TFTP and NNTP — no authentication or encryption at all
HTTPS, SSH, and SFTP protect your data even if packets are captured.
Why sniffers are hard to detect
Sniffers work at the data link layer (Layer 2) of the OSI model. Since OSI layers are independent, upper layers including your browser and apps have no awareness that sniffing is happening beneath them.
Passive sniffing is especially invisible. There are no extra packets, no anomalies in traffic patterns, no error logs. The only way to detect it is to scan the network for NICs running in promiscuous mode which requires active monitoring tools and someone actually looking. Most networks have neither.
Hardware analyzers and SPAN ports

A hardware protocol analyzer is a physical device that captures traffic without affecting it. It handles high-traffic loads without dropping packets but is expensive mostly used by enterprises.
A SPAN port (port mirroring) copies all switch traffic to one port for monitoring. Network administrators use SPAN ports to connect security tools and intrusion detection systems. But if an attacker gains access to a SPAN port, they can see all traffic on the entire network making SPAN port access one of the most dangerous footholds an attacker can establish.
Wiretapping
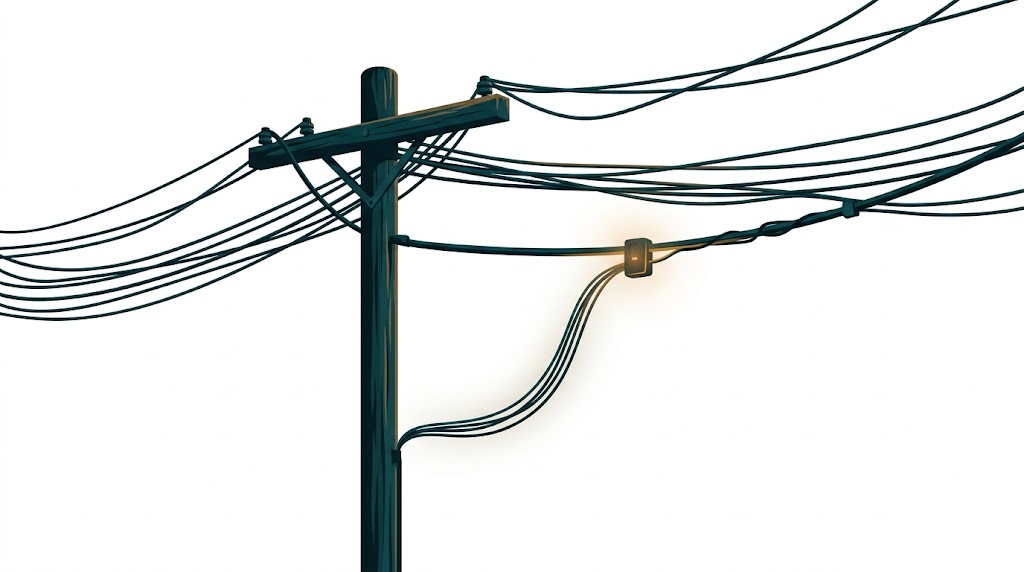
Wiretapping is the interception of communications by connecting a listening device to the line. It works across telephone systems, internet connections, and any physical communication medium. Two types:
Active wiretapping — attacker can monitor, record, and also alter or inject data (a MITM attack)
Passive wiretapping — attacker only listens and records without altering anything
Lawful Interception (LI) is the legal version used by law enforcement with proper authority, covering VoIP, traditional calls, and internet communications. The network operator is legally required to provide access under LI orders. Unauthorized wiretapping is a criminal offense in most countries regardless of intent.
Want to dive deeper?
Explore our certified internship and certification programs related to this topic.

Edwin Saji
Intern at Edwhere