VLAN Hopping: Understanding Switch Spoofing and Double Tagging

You split your network into VLANs to keep departments separate. Finance on one. Engineering on another. The idea is simple what happens in VLAN 10 stays in VLAN 10. But when a switch is misconfigured, that wall disappears. An attacker with basic knowledge and the right technique can cross from one VLAN into any other on the network. No firewall bypass needed. No special exploit. Just a poorly configured trunk port and a double-tagged Ethernet frame.
This is VLAN hopping and it is one of the most underestimated threats in modern enterprise networks.
What is a VLAN and Why Does Segmentation Matter?
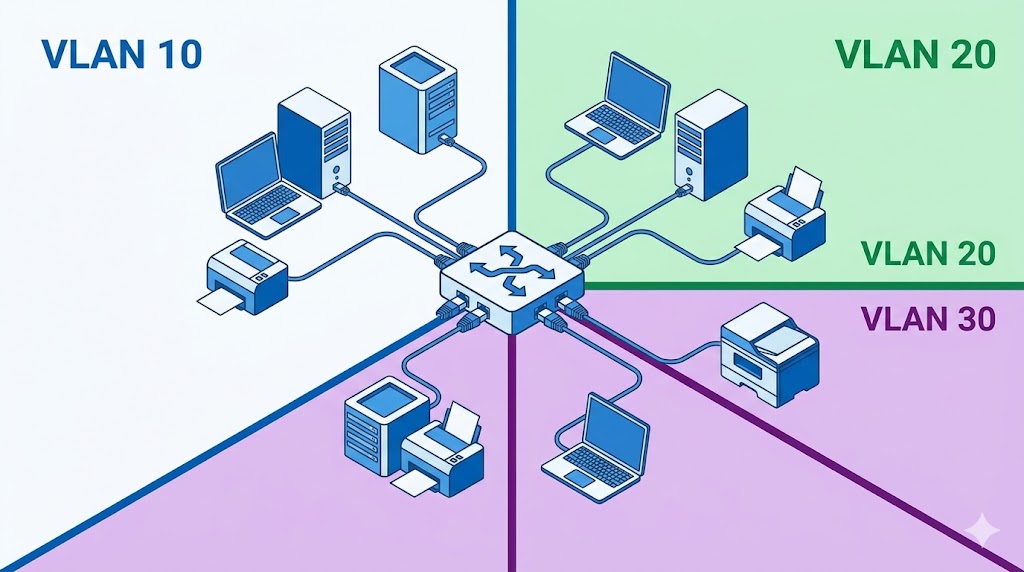
A VLAN (Virtual Local Area Network) is a logical grouping of devices on a network, regardless of their physical location. VLANs allow network administrators to segment traffic so that devices in one VLAN cannot directly communicate with devices in another without going through a router or layer 3 switch.
This segmentation is a critical security control. It keeps sensitive traffic finance records, server communications, management interfaces isolated from general user traffic. A device on the HR VLAN should never see packets addressed to the database VLAN.
VLAN tagging, defined by the IEEE 802.1Q standard, is how switches identify which VLAN a packet belongs to. When a frame travels across a trunk link a connection that carries traffic from multiple VLANs between switches a VLAN tag is inserted into the Ethernet frame header identifying which VLAN it belongs to. When it reaches the destination switch, the tag is read, the frame is forwarded to the correct VLAN, and the tag is stripped before delivery.
The native VLAN is the VLAN assigned to frames arriving on a trunk port without a tag. By default, this is VLAN 1 on most Cisco switches. This default configuration is the root cause of one of the most common VLAN hopping vulnerabilities.
VLAN Hopping: Breaking the Boundaries

VLAN hopping is a network attack that allows an attacker to gain unauthorized access to resources on a VLAN they should not be able to reach. The goal is to bypass network segmentation controls entirely the very controls put in place to isolate traffic for security and management reasons.
A successful VLAN hopping attack can allow an attacker to steal sensitive information, modify or delete data, install malicious code, and spread malware across the network. There are two methods used to perform it.
Method 1: Switch Spoofing
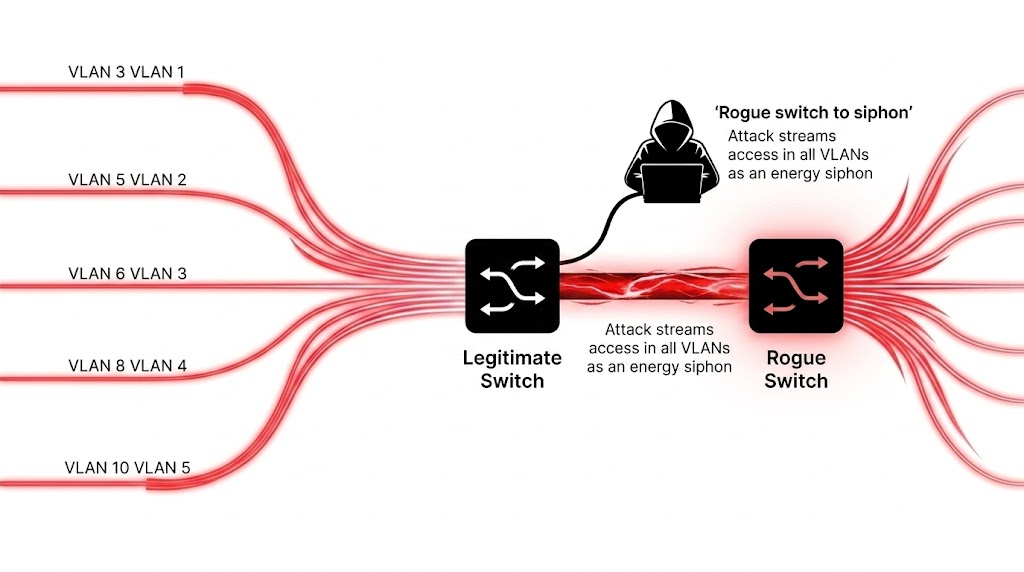
Switch spoofing exploits the DTP (Dynamic Trunking Protocol) feature present on many Cisco switches. DTP allows switches to automatically negotiate whether a port should operate as an access port or a trunk port. This is convenient for administrators but dangerous when enabled on user-facing ports.
The attacker connects a rogue switch to the network and sends DTP negotiation messages to the legitimate switch on the other end. If the legitimate switch’s port is configured in dynamic auto or dynamic desirable mode, it will respond to the negotiation and establish a trunk link with the rogue switch. Once a trunk link is established, the attacker’s rogue switch receives traffic from all VLANs passing through that trunk not just the one they are supposed to be on.
The attack is silent and does not generate unusual traffic patterns on its own, making it difficult to detect without specific monitoring for DTP negotiation on end-user ports.
Method 2: Double Tagging
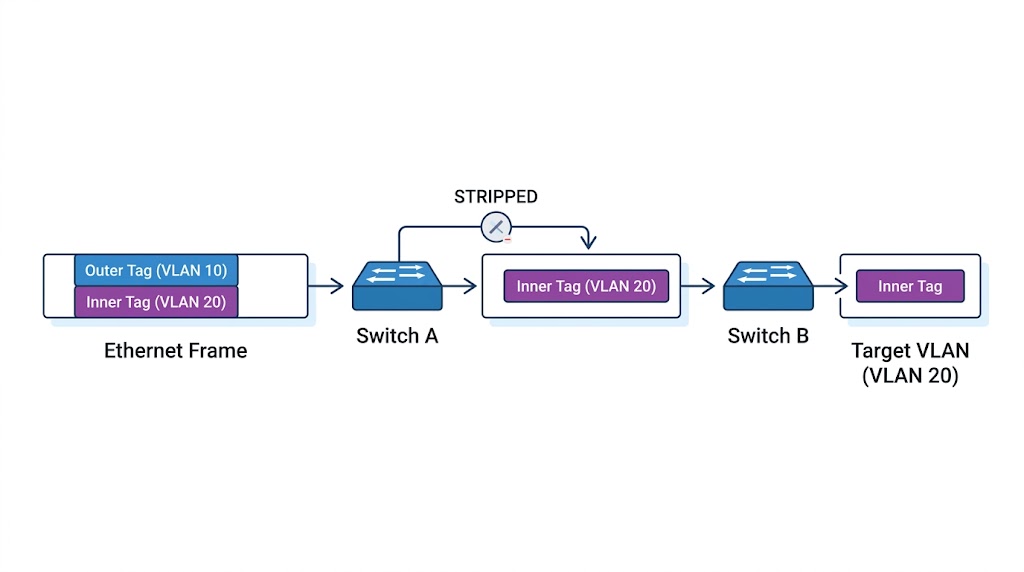
Double tagging is more surgical. The attacker crafts Ethernet frames with two 802.1Q VLAN tags an outer tag and an inner tag.
The outer tag matches the native VLAN of the first switch typically VLAN 1. The inner tag contains the VLAN ID of the target VLAN the attacker wants to reach.
Here is what happens step by step. The attacker sends the double-tagged frame to the first switch. The switch reads the outer tag, recognises it as the native VLAN, strips the outer tag, and forwards the frame out all trunk interfaces because the native VLAN is not tagged on trunk ports by default. The frame now only carries the inner tag. When it arrives at the second switch, that switch reads the inner tag and delivers the frame to the target VLAN.
The victim on the target VLAN receives a packet from the attacker with no indication that it crossed a VLAN boundary. The attacker cannot receive replies directly this is a one-way attack but it is enough to send malicious payloads, trigger downloads, or execute specific commands on target systems.
This attack only works when switch ports are configured to use native VLANs and those native VLANs are not explicitly tagged.
STP Attack: Becoming the Root Bridge
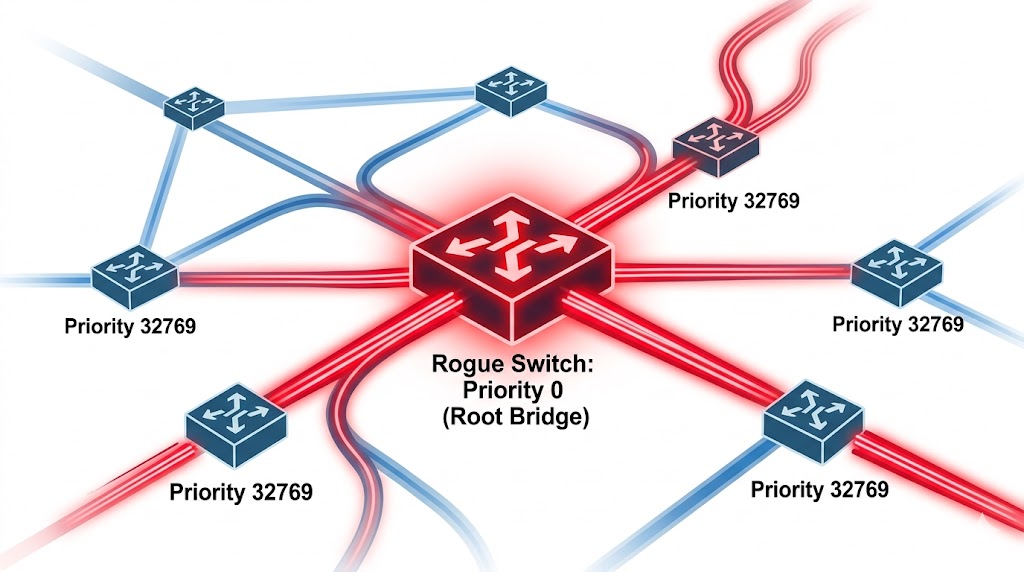
A related attack worth understanding is the STP attack Spanning Tree Protocol attack. STP is used in LAN-switched networks to prevent routing loops by electing a root bridge that all other switches build their paths around. The root bridge is selected based on Bridge Priority the switch with the lowest Bridge Priority value wins. The default Bridge Priority is 32769.
An attacker with access to two switches introduces a rogue switch configured with a Bridge Priority of 0. This is lower than any legitimate switch in the network. The rogue switch wins the root bridge election, and all traffic in the network is rerouted through it. The attacker now sits in the path of all network traffic and can capture everything flowing across the infrastructure.
How to Defend Against MAC Spoofing
Before covering VLAN hopping defenses, it is worth understanding the defenses against MAC spoofing since they share the same infrastructure controls. The most effective combination is three layered features working together:
• DHCP Snooping Binding Table — filters untrusted DHCP messages and builds a binding table of MAC address, IP address, lease time, VLAN number, and interface. Acts as a firewall between untrusted hosts and DHCP servers
• Dynamic ARP Inspection — checks IP-to-MAC address bindings for each ARP packet and automatically drops invalid bindings
• IP Source Guard — restricts IP traffic on untrusted layer 2 ports by filtering based on the DHCP snooping binding table, preventing IP address spoofing
• IEEE 802.1X — port-based Network Access Control that enforces authentication at the point where a user joins the network
• Port Security — limits the number of MAC addresses allowed on a port and specifies which addresses can be permitted
How to Defend Against VLAN Hopping
Defending Against Switch Spoofing
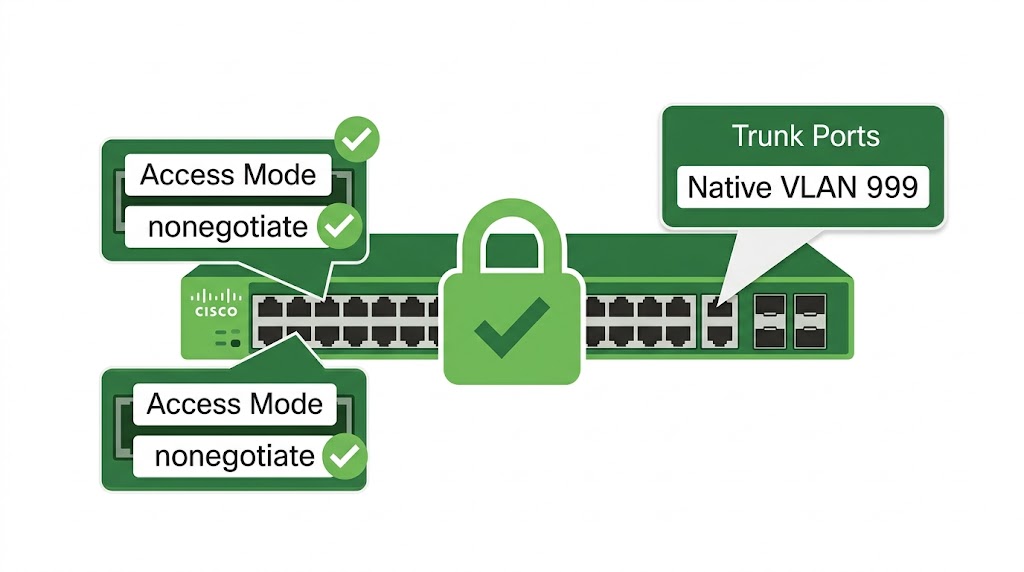
The fix is straightforward: remove DTP negotiation from all ports that should never become trunk links. Explicitly configure access ports and disable trunking negotiation on them.
switchport mode accessswitchport mode nonegotiateFor trunk ports, also disable auto-negotiation to prevent a rogue device from negotiating a trunk link:
switchport mode trunkswitchport mode nonegotiateDefending Against Double Tagging
Three configuration changes eliminate the double tagging vulnerability:
First, specify the default VLAN used when the interface stops trunking. This ensures all access ports fall back to a known, controlled VLAN:
switchport access vlan 2Second, change the native VLAN on all trunk ports from the default VLAN 1 to an unused VLAN ID. This removes the overlap between the attacker’s native VLAN and the trunk’s native VLAN that double tagging requires:
switchport trunk native vlan 999Third, explicitly tag all native VLAN traffic on trunk ports. This means the switch will tag native VLAN frames before forwarding them, making double tagging impossible because the attacker’s outer tag will no longer match an untagged native VLAN:
vlan dot1q tag nativeAdditional measures include configuring private VLANs to isolate ports from each other on the same VLAN, and regularly auditing VLAN and switch configurations to ensure compliance with security policies.
Want to dive deeper?
Explore our certified internship and certification programs related to this topic.

Edwin Saji
Intern at Edwhere