EDWHERE BLOG
Master the art of technical problem solving with our expert-led walkthroughs and deep dives.

Cybersecurity
Apr 24, 2026
Nmap Cheat Sheet 2026: Every Command You Need for Network Scanning
Edwin Saji
Read More

Cybersecurity
Apr 22, 2026
Inside an IoT Attack: How Smart Devices Get Hacked
Edwin Saji
Read More

Cybersecurity
Apr 22, 2026
How Hackers Use Wireshark to Capture Passwords and Network Data
Edwin Saji
Read More

Cybersecurity
Apr 16, 2026
VLAN Hopping: Understanding Switch Spoofing and Double Tagging
Edwin Saji
Read More
Cybersecurity
Apr 16, 2026
ARP Poisoning, MAC Spoofing & MITM Attacks Explained
Edwin Saji
Read More

Cybersecurity
Apr 13, 2026
DHCP Attacks Explained: How Attackers Starve Your Network and Take Control (2026)
Edwin Saji
Read More

Cybersecurity
Apr 9, 2026
CAM Table Attacks: How Attackers Break Switched Networks
Edwin Saji
Read More

Cybersecurity
Apr 9, 2026
Network Sniffing : Hubs, Switches & How Attackers Intercept Your Data
Edwin Saji
Read More

Cybersecurity
Apr 8, 2026
Cybersecurity Job Roles: What You Can Become (2026)
Edwin Saji
Read More

Cybersecurity
Apr 8, 2026
How AI is Changing Cybersecurity in 2026
Edwin Saji
Read More
Cybersecurity
Apr 7, 2026
Bug Bounty Hunting: A Beginner's Complete Guide (2026)
Edwin Saji
Read More
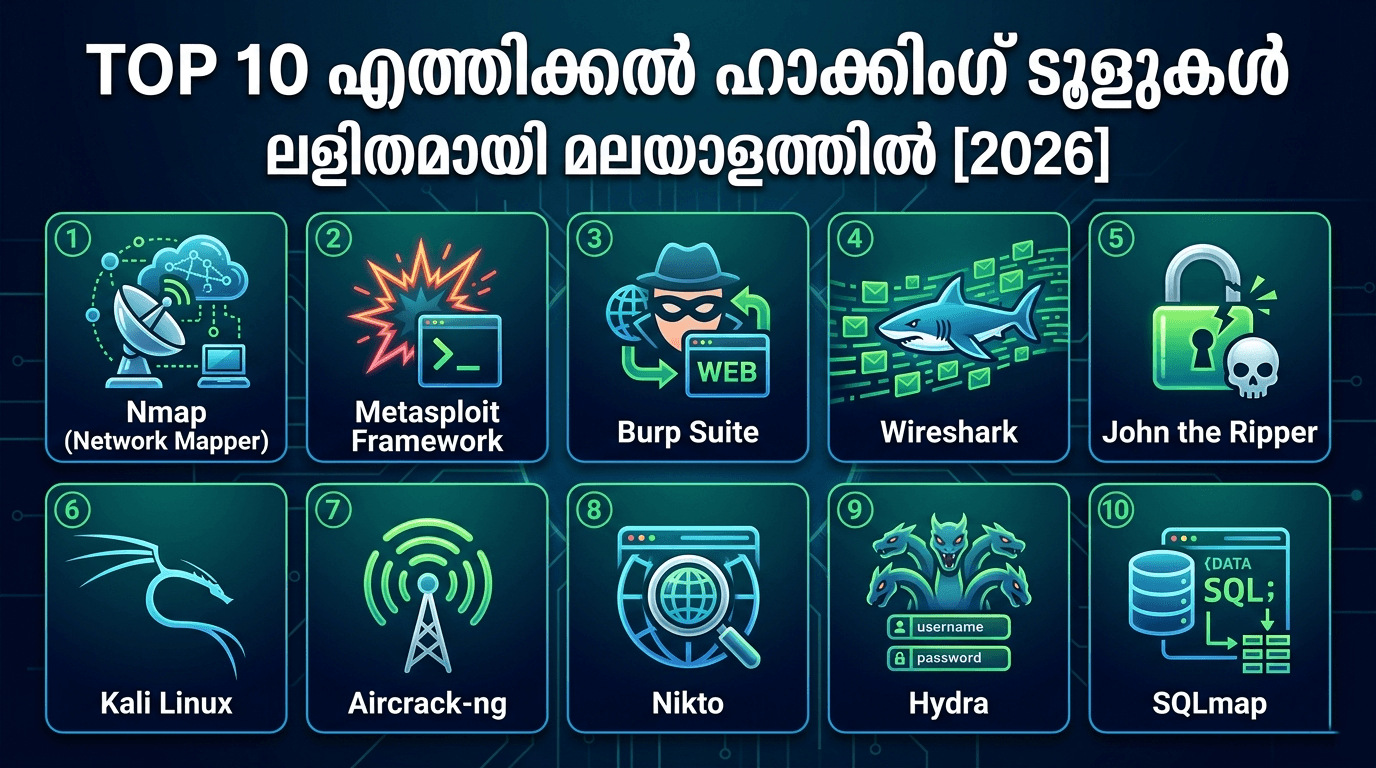
Cybersecurity
Mar 27, 2026
Top 10 Ethical Hacking Tools 2026 Explained in Malayalam
Melbin Johny
Read More
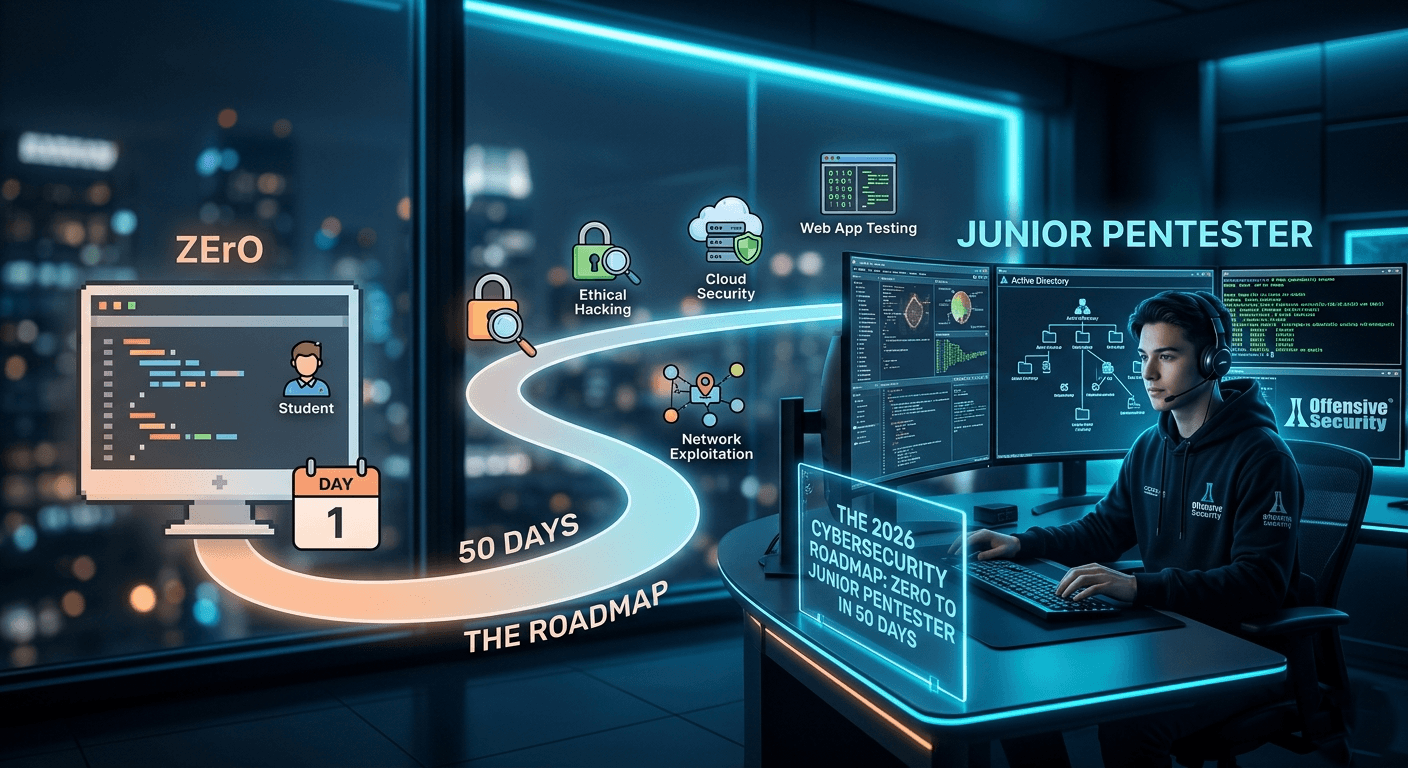
Cybersecurity
Mar 26, 2026
The 50-Day Junior Pentester Roadmap (2026)
Melbin Johny
Read More

Cybersecurity
Mar 25, 2026
Best Hacking Course in Malayalam: Start Your Cyber Security Career!
Melbin Johny
Read More

Cybersecurity
Mar 25, 2026
How to Start a Cyber Security Career with 50-Day Challenge
Melbin Johny
Read More